ZOOT NATIVE + 固定IP をVyOS で使う
ZOOT NATIVE + 固定IP とは
InterLink の提供するIPoE 接続サービスです。IPv4 over IPv6 技術でありながら固定グローバルIPアドレス1個(IPv4) を公開できます。
VyOS を立ち上げる
新規セットアップについてはコチラ VyOS セットアップ
ほぼコチラを参考にしました。Qita - VyOSからtransix ipv4接続(固定ip)を使う Special thanks!
当環境
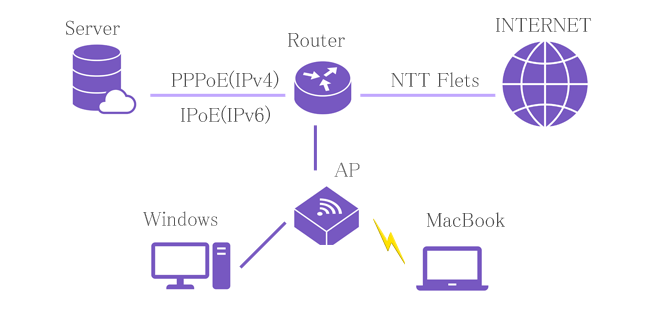
Router: NTT Flets PR-400NE (PPPoE pass through, 192.168.8.1)
│
├─ Server: Ubuntu server 22.04 (192.168.8.3 gw 192.168.8.10)
│ ├─ kvm
│ │ ├─ VyOS2(PPPoE, 192.168.8.9, Via provider) *1
│ │ └─ VyOS4(IPoE, 192.168.8.10, IPv4 over IPv6 on transix, DHCP server)
│ └─ LXD container
│ ├─ DNS2(192.168.8.7, gw 192.168.8.9) *1
│ ├─ DNS4(192.168.8.27, gw 192.168.8.10)
│ ├─ Web2(192.168.8.74, gw 192.168.8.9) *1
│ ├─ Web4(192.168.8.75, gw 192.168.8.10)
│ ├─ Mail2(192.168.8.8, gw 192.168.8.9) *1
│ └─ Mail4(192.168.8.28, gw 192.168.8.10)
│
└─ AP: 11ac Wifi
├─ Desktop PC: Windows11(192.168.8.153, gw 192.168.8.10 DHCP client)
└─ Note PC: MacBook(192.168.8.154, gw 192.168.8.11 DHCP client)
*1) Once the IPoE connection is stable, stop PPPoE.
現在、ZOOT NEXT(PPPoE接続 固定IPv4 1個 GW 192.168.8.9)を利用しています。VyOS で安定しているので触らずに。ZOOT NATIVE 接続用に新たなVyOS (KVMゲスト) を立ち上げます(ZOOT NEXT とZOOT NATIVE は同時に使えます)。IPoE が安定したら、PPPoEは停止します。
VyOSを設定する
Interface を設定
interfaces {
ethernet eth0 {
address 2400:XXXX:XXXX:2100::feed/64 // Prefix + ::feed
address 192.168.8.10/24
dhcpv6-options {
parameters-only
}
hw-id XX:XX:XX:XX:XX:XX
ipv6 {
address {
autoconf
}
}
policy {
route transix
}
}
tunnel tun0 {
address 130.XXX.XXX.146/32 // My global IP
encapsulation ipip6
mtu 1454
remote 2200:XXXX::feed:143 // transix IP
source-address 2400:XXXX:XXXX:2100::feed // eth0 IPv6
}
}
policy を設定。
SYNパケット(外向けの最初)でMSSを上書きする。ethernet デバイスに設定する(tunnel デバイスでは動作しなかった)。
# MSS = MTU - 40
policy {
route transix {
rule 10 {
destination {
address 0.0.0.0/0
}
protocol tcp
set {
tcp-mss 1414
}
tcp {
flags {
not {
ack
fin
rst
}
syn
}
}
}
}
}
protocols を設定(static route)
protocols {
static {
route 0.0.0.0/0 {
interface tun0 {
}
}
route 192.168.8.0/24 {
interface eth0 {
}
}
}
}
Firewall を設定。
firewall {
global-options {
all-ping enable
broadcast-ping disable
}
group {
address-group MyIP {
address 139.XXX.XXX.105
address 139.XXX.XXX.86
}
}
ipv6 {
ipv6-name accept_all_v6 {
default-action accept
rule 2 {
action drop
state {
invalid enable
}
}
}
ipv6-name public_to_local_v6 {
default-action drop
rule 1 {
action accept
state {
established enable
related enable
}
}
rule 2 {
action drop
state {
invalid enable
}
}
rule 3 {
action accept
protocol icmpv6
}
}
ipv6-receive-redirects disable
ipv6-src-route disable
ip-src-route disable
log-martians enable
name accept_all {
default-action accept
rule 2 {
action drop
state {
invalid enable
}
}
}
name public_to_local {
default-action drop
rule 1 {
action accept
state {
established enable
related enable
}
}
rule 2 {
action drop
state {
invalid enable
}
}
rule 3 {
action accept
protocol icmp
}
}
name public_to_private {
default-action drop
rule 3 {
action accept
state {
established enable
related enable
}
}
rule 4 {
action drop
state {
invalid enable
}
}
rule 22 {
action accept
description SSH
destination {
port 22
}
protocol tcp
source {
group {
address-group MyIP
}
}
}
rule 53 {
action accept
description dns
destination {
port 53
}
protocol udp
}
rule 80 {
action accept
description http
destination {
port 80
}
protocol tcp
}
}
receive-redirects disable
send-redirects enable
source-validation disable
syn-cookies enable
twa-hazards-protection disable
zone local {
default-action drop
from private {
firewall {
ipv6-name accept_all_v6
name accept_all
}
}
from public {
firewall {
ipv6-name public_to_local_v6
name public_to_local
}
}
local-zone
}
zone private {
default-action drop
from local {
firewall {
ipv6-name accept_all_v6
name accept_all
}
}
from public {
firewall {
ipv6-name public_to_local_v6
name public_to_private
}
}
interface eth0
}
zone public {
default-action drop
from local {
firewall {
ipv6-name accept_all_v6
name accept_all
}
}
from private {
firewall {
ipv6-name accept_all_v6
name accept_all
}
}
interface tun0
}
}
NAT を設定(SNAT, DNAT)
nat {
destination {
rule 22 {
description SSH
destination {
port 22
}
inbound-interface tun0
protocol tcp
translation {
address 192.168.8.3
}
}
rule 53 {
description dns
destination {
port 53
}
inbound-interface tun0
protocol udp
translation {
address 192.168.8.27
port 1053
}
}
rule 80 {
description HTTP
destination {
port 80
}
inbound-interface tun0
protocol tcp
translation {
address 192.168.8.75
}
}
}
source {
rule 20 {
description "eth0 => tun0"
outbound-interface tun0
source {
address 192.168.8.0/24
}
translation {
address masquerade
}
}
}
}
DHCP server を設定
service {
dhcp-server {
shared-network-name NTT_NETWORK {
subnet 192.168.8.0/24 {
default-router 192.168.8.10
lease 86400
name-server 192.168.8.10
range 0 {
start 192.168.8.150
stop 192.168.8.220
}
}
}
}
}
これでルーターとAP の配下に繋がるデバイスは、192.168.8.0/16 のIP アドレスが振られ、Gateway 192.168.8.10、transix 通じてインターネットに繋がります。